WELCOME TO CRONINITY
 |  |  |
|---|---|---|
 |  |  |
Security Logging - Parent Events versus Base Events
Parent Events versus Base Events Concept The diagram below highlights the SOC Triad, with core cybersecurity tools like Network Detection...
Elastic - Visualizations - Reusing Dashboards with controls and Markdowns
If you have the same dashboard content you want to display across multiple similar but different items, it can be extremely cumbersome to...
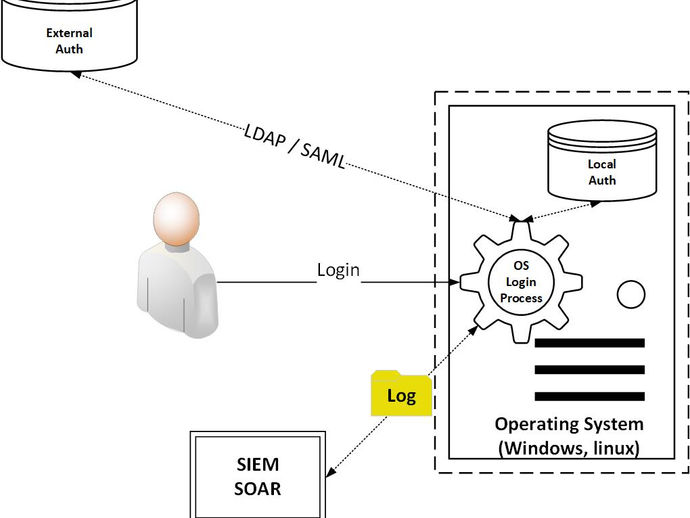
Connecting Logs to Identities in devices and Applications
Authentication Logging for Operating Systems Overview One crucial aspect of cybersecurity involves monitoring logins associated with user...
Elastic Security - Random Notes and Links
Elastic - Overview When considering data storage in Elasticsearch, it's common to think of relational databases. However, Elasticsearch...
Logging Systems - Logging Ain't Easy But it's Necessary
NIST 800-53 logging controls are primarily categorized within the AU (Audit and Accountability) control family. Within AU, there are...
Cybersecurity Logging Systems - C.E.S 'Crowdstrike, Elastic, Splunk'
In cybersecurity, various logging systems are employed, often known as 'Security Information & Event Management' (SIEM) systems when...